Mongolian Certificate Authority Hacked to Distribute Backdoored CA Software

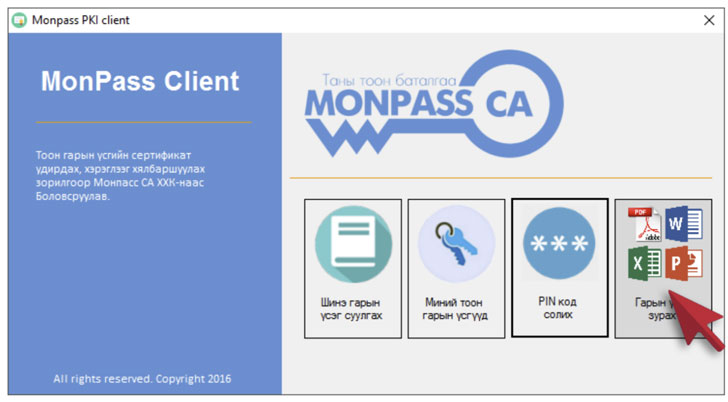
In yet another instance of software supply chain attack, unidentified hackers breached the website of MonPass, one of Mongolia's major certificate authorities, to backdoor its installer software with Cobalt Strike binaries.
The trojanized client was available for download between February 8, 2021, and March 3, 2021, said Czech cybersecurity software company Avast in a report published Thursday.
In addition, a public webserver hosted by MonPass was infiltrated potentially as many as eight separate times, with the researchers uncovering eight different web shells and backdoors on the compromised server.
Avast's investigation into the incident began after it discovered the backdoored installer and the implant on one of its customers' systems.
"The malicious installer is an unsigned [Portable Executable] file," the researchers said. "It starts by downloading the legitimate version of the installer from the MonPass official website. This legitimate version is dropped to the 'C:\Users\Public\' folder and executed under a new process. This guarantees that the installer behaves as expected, meaning that a regular user is unlikely to notice anything suspicious."
The modus operandi is also notable for the use of steganography to transfer shellcode to the victim machine, with the installer downloading a bitmap image (.BMP) file from a remote server to extract and deploy an encrypted Cobalt Strike beacon payload.
MonPass was notified of the incident on April 22, after which the certificate authority took steps to address their compromised server and notify those who downloaded the backdoored client.
The incident marks the second time software provided by a certificate authority has been compromised to infect targets with malicious backdoors. In December 2020, ESET disclosed a campaign called "Operation SignSight," wherein a digital signature toolkit from the Vietnam Government Certification Authority (VGCA) was tampered to include spyware capable of amassing system information and installing additional malware.
The development also comes as Proofpoint, earlier this week, revealed the abuse of Cobalt Strike penetration testing tool in threat actor campaigns has shot through the roof, jumping 161% year-over-year from 2019 to 2020.
"Cobalt Strike is becoming increasingly popular among threat actors as an initial access payload, not just a second-stage tool threat actors use once access is achieved, with criminal threat actors making up the bulk of attributed Cobalt Strike campaigns in 2020," Proofpoint researchers said.

 gnidovsky
gnidovsky 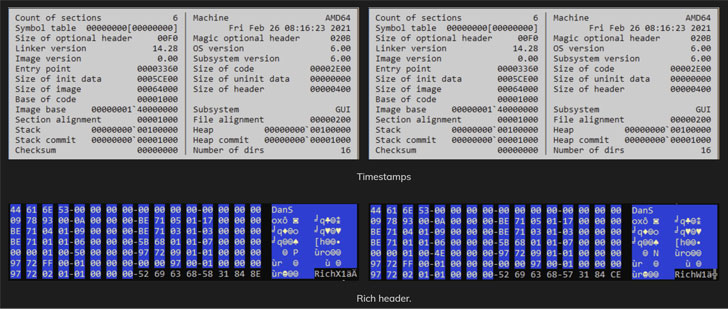























![Cyber Security, Blockchain Technology and Ecosystem [2021-2022]](https://media4.giphy.com/media/ezwqkPUbS68IasOETK/giphy.gif?cid=790b7611ee75cd87d925b93e7572b8318d66c434150abc52&rid=giphy.gif&ct=g)